Intellenet, the seemingly online network, has long been hailed as its boundless potential. Individuals pour into this digital haven, seeking connection, information, and limitless possibilities. However, beneath the surface of this utopian facade lie rumors about Intellenet's true nature.
Leaked documents paint a disturbing picture of a system rife with deceit. Individuals are exploited by Intellenet to fuel a hidden agenda, that could reshape the very fabric of our existence. The truth about Intellenet is more complex than we understand, and it's time to shed light on its nefarious intentions.
The evidence is mounting. Information is controlled through Intellenet, dictating our actions. Our freedoms are eroded, and we are trapped within a digital prison.
This expose will reveal the truth. Be prepared to have your worldview shattered. The truth is out thereawaiting discovery.
The Detective and the Virtual Menace: An Interweb Inquiry
Detective Malone squinted at his monitor, the flickering glow reflecting in his weary eyes. The cybercrime unit had called him in on this one - a perpetrator buried deep within the Intellenet, manipulating data like a puppeteer pulling strings. His case files were sparse, fragments scattered across encrypted servers, each a cryptic puzzle piece leading to a shadowy figure known only as "The Weaver". Malone felt a familiar tug of adrenaline, his instincts screaming that this was no ordinary cyber theft. This was a game of cat and mouse, played out in the digital ether, and he was determined to catch the prey.
- Code weaponry
- Darknet forums
Malone knew that time is of the essence. Every minute The Oracle remained free, more lives were at risk. This wasn't just about chasing a digital ghost; it was about protecting information itself.
Tracking the Virtual Trail: An Insider's Look at Unveiling Cyber Identities
In the labyrinthine world of the internet, identities can be as fluid and ambiguous as smoke. For investigators strive to pierce the veil of anonymity, traditional strategies fall inadequate. It requires a unique set of skills and expertise - an intimate grasp with the ever-shifting landscape of online activities. This is where the art of Intellenet comes into play.
- Revealing online identities requires a deep dive into digital footprints, analyzing patterns in messaging apps activity, and understanding the nuances of cyberculture.
- Sophisticated investigators utilize specialized tools to gather data, trace connections, and uncover hidden relationships between users.
- The key lies in understanding the psychology behind online personas, deciphering the subtle messages embedded within text, images, and even multimedia content.
Intellenet is not simply about accessing systems; it's about analyzing the vast amounts of data generated in the digital realm. It's a continuous process that demands constant improvement.
Intelligent Connections: Charting a Course Through Cyberspace
Unraveling the intricate links of the modern digital landscape is a complex endeavor. All click, transaction leaves a subtle impression on the vast matrix of data. Intellenet Threads delve into these subtleties, revealing hidden insights about our digital activities. By analyzing the stream of data, we can begin to grasp the complex landscape that shapes our online world.
- From social media activity to online transactions, Intellenet Threads sheds light on the ever-evolving stories that define our digital journeys.
- Unmasking the code of the internet, Intellenet Threads offers a unique perspective on the world we create online.
Engage us as we journey into the fascinating world of more info Intellenet Threads and reveal the hidden connections that lie within the digital landscape.
Virtual Veils: Cracking this Code of Intellenet Investigations
The intellenet, a labyrinth of interconnected platforms, cloaks itself in layers of virtual veils, designed to obscure evidence. Digital specialists must navigate this complex terrain, utilizing advanced methods to penetrate these veils and uncover the hidden secrets. Sophisticated attackers leverage anonymity and encryption in order to mask their actions, creating a constant cat-and-mouse game between investigators and criminals. Cracking these virtual veils requires a combination of technical expertise, critical thinking, and an unwavering resolve to unravel the truth that lie within.
- Intelligence officers meticulously analyze network traffic, log files, and other digital traces, searching for anomalies or patterns that indicate malicious activity.
- Advanced encryption techniques can be used to protect sensitive data, but investigators may employ countermeasures to gain access to encrypted information.
- Open-source intelligence|Social media analysis provides a valuable source of information, allowing investigators to uncover clues that might otherwise remain undetected.
Unveiling the Firewall: Intrigue, Intrigue, and the P.I.'s Dilemma
The digital age has thrown a wrench into the classic detective's toolbox. Where once footprints led to a suspect and phone calls held whispered secrets, now encrypted messages dance across firewalls and rogue algorithms weave complex webs of lies. For the Private Investigator, this means stepping out from behind their familiar office walls and into a world where every byte is a clue and every connection could be a trap. It's a thrilling, terrifying new landscape, one where trust is fragile, and truth hides in the binary of the digital realm. The line between good and evil has become blurred, and only the most resourceful P.I. can navigate this labyrinth of information.
 Tia Carrere Then & Now!
Tia Carrere Then & Now! Alana "Honey Boo Boo" Thompson Then & Now!
Alana "Honey Boo Boo" Thompson Then & Now!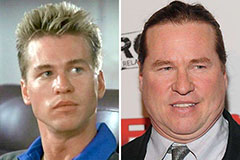 Val Kilmer Then & Now!
Val Kilmer Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Susan Dey Then & Now!
Susan Dey Then & Now!